Over the past 20 years, we have seen the server become a normal fixture in the Small Business environment. At times there have been multiple servers handling file storage, email and printer sharing.
In the past decade we have helped migrate the mail to the cloud, as Office 365 has blossomed into one of, if not, the largest online mail service. The subscription service for the Office software was next, eliminating the need for CDs and Product Keys.
The latest is the OneDrive attack against Google Docs and Google Drive. Now Office on the Web is mainstream and sharing a Word doc is a breeze. 1Tb of storage comes with nearly every flavor of 365, and adding a 365 Group yields yet another terabyte. Laptops with limited storage are no longer a pain to use, as everything is available, by connecting to the cloud.
So where does this lead our businesses?
Printers that connect wirelessly or via Ethernet are standard these days, and sharing them from a central server is not as necessary as it was when we used serial cables or USB connections. The mail and the files are “up there,” so what’s left? SECURITY.
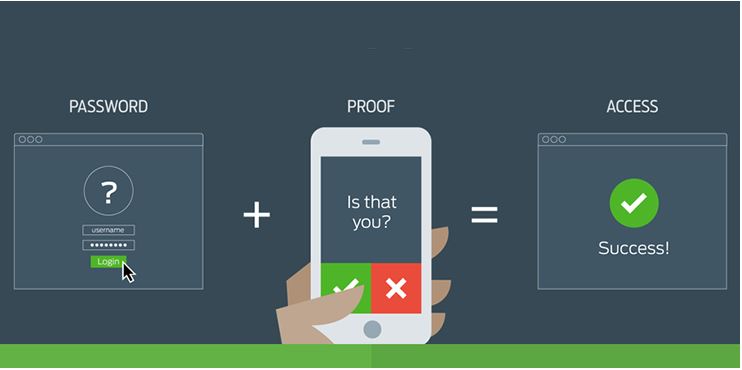
Without central management of network security, we return to the dark ages. We were forced to create user accounts on multiple devices to share printers and keep the passwords consistent. If you forgot your password, you had better know the admin password. Security was more of a speed bump we had to deal with, rather than a lifesaver for our business and reputations.
Microsoft is moving businesses to the Azure Active Directory. With your AD in the cloud, the last need for a physical server evaporates. When will this become mainstream for the SMB space? Not today or tomorrow. There are other challenges, such as software that must be shared locally, but keep watching. Your business has evolved in your industry… and it continues to evolve in IT. We’re happy to come along for the ride.